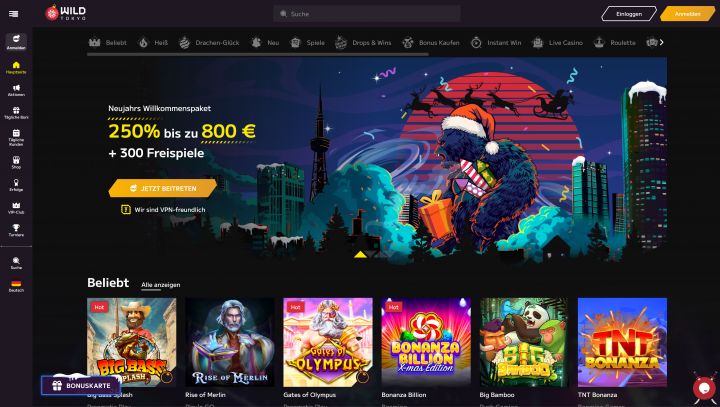
When it comes to internet gaming, Wild Tokyo Casino Login Mobile, safety is paramount, especially for Canada-based players of Wild Tokyo Casino. We find that this platform employs a variety of methods to ensure the security of its sign-in processes. From 2FA to advanced encryption standards, these methods are intended to protect player information. However, there's more to this story than meets the eye, and understanding the full extent of these measures can uncover key understandings into user security.
Overview of Tokyo Wild Casino Safety Measures
When we examine the safety measures at Wild Tokyo Casino, it’s important to recognize the combination of modern technology and conventional techniques to establish a comprehensive protection system. These methods are designed with a dual aim—protecting user confidentiality and guaranteeing efficient reaction to incidents. Employing state-of-the-art coding and live surveillance, the gambling house safeguards sensitive information from potential breaches. At the same time, conventional security procedures, such as monitoring and on-site staff, reinforce these online protections. An effective incident response team is also vital, quickly addressing any questionable activity and minimizing risks to user confidentiality. By melding these strategies, Wild Tokyo Casino maintains a strong safety stance that not only prevents threats but also fosters a trusted environment for its customers.
Safe Sign-In Procedures
In our analysis of secure login protocols, we must evaluate the essential components that secure user accounts at Wild Tokyo Casino. Utilizing two-factor authentication boosts security substantially, while encoded data transmission confirms that confidential information stays private. Additionally, implementing robust password practices can mitigate the risk of unapproved access, making these measures crucial for upholding the soundness of the casino's online systems.
Two-Factor Authentication Benefits
While some might undervalue the significance of safe login protocols, adopting two-factor authentication (2FA) can significantly enhance our defense against unapproved access. 2FA demands not only a password but also a additional verification method, elevating our security understanding. This multi-layered approach reduces risks connected with breached credentials, especially in an era of rising cyber threats.
Moreover, implementing 2FA doesn't have to detract from the user experience; rather, it can boost it. When users realize that their accounts are better protected, it cultivates confidence, creating a sense of security. We should also analyze the simplicity of implementing various 2FA methods—such as SMS codes or authenticator apps—guaranteeing that heightened security doesn't come at the cost of usability.
Encrypted Data Transmission
Securing user data during transmission is crucial for maintaining the integrity of our login protocols. To achieve this, we must employ encrypted communications, which convert sensitive information into unreadable formats during transit. This ensures that even if data is intercepted, it remains protected. Utilizing secure channels, such as HTTPS, provides an additional layer of encryption, safeguarding our authentication credentials from potential threats. By analyzing the encryption standards like TLS (Transport Layer Security), we gain insights into how these protocols mitigate the risk of data breaches. It’s essential to continuously update and refine our encryption practices to address evolving security threats. Ultimately, robust encrypted data transmission reinforces user trust and enhances the overall security framework of our online platforms.
Secure Password Practices
As encrypted data transmission protects sensitive information during transfer, secure password practices form the backbone of our authentication protocols. To ensure robust security, we must prioritize password strength. It’s critical that our passwords are lengthy, incorporating a mix of upper and lower case letters, numbers, and special characters. This complexity significantly reduces vulnerability to attacks. Moreover, utilizing password managers can effectively enhance our security strategy. These tools not only generate strong passwords but also securely store them, eliminating the temptation to reuse easily guessed passwords. By adhering to these methodologies, we reinforce our login security, safeguarding our data against unauthorized access. Embracing secure password practices is essential in today’s digital landscape, enabling us to navigate online spaces with confidence.
Encryption Standards in Use
In our analysis of the Wild Tokyo Casino's cryptographic standards, we must consider the application of SSL/TLS protocols as a fundamental security procedure. By analyzing the diverse data encryption techniques used, we can assess their efficacy in lessening risks. Additionally, comprehending how Secure Socket Layer technology is applied will clarify the general integrity of the casino's digital communications.
SSL/TLS Protocol Implementation
While many online platforms prioritize user safety, the application of SSL/TLS protocols at Wild Tokyo Casino functions as a essential backbone for secure communications. We must recognize the significance of using the newest TLS versions to reduce risks linked to SSL vulnerabilities. Outdated versions, such as SSL 3.0, are infamous for security flaws that jeopardize data integrity and confidentiality. By complying with stringent protocols and utilizing forward secrecy, Wild Tokyo Casino successfully safeguards user transactions against prospective breaches. Moreover, regular updates and thorough testing of these protocols secure that the casino remains resilient against new threats. For those focused about online security, comprehending the nuances of SSL and TLS implementation is crucial for navigating possible vulnerabilities efficiently.
Data Encryption Techniques

Given the rising sophistication of cyber threats, using strong data encryption methods is essential at Wild Tokyo Casino. We've adopted sophisticated encryption algorithms, such as AES (Advanced Encryption Standard) and RSA, to secure that both sensitive user data and transaction information stay secure. These algorithms offer superior levels of security and efficiency, enabling us to maintain data integrity throughout our operations.
To achieve this, we implement 256 bit encryption for data stored and in transit, reinforcing our commitment to protecting player information from unpermitted access. Regular audits and updates of our encryption standards are crucial, ensuring we stay ahead of new vulnerabilities. In doing so, we foster a secure environment where players can interact securely, knowing their data is shielded by advanced encryption techniques.
Secure Socket Layer Usage
Robust encryption mechanisms like those detailed previously are complemented by our use of Secure Socket Layer (SSL) protocols. SSL benefits are manifold; it not only encrypts data in transit, preventing interception by nefarious actors, but also provides authentication, ensuring users connect to the intended server. This two-tiered defense bolsters our commitment to safeguarding private information.
However, we must acknowledge potential SSL vulnerabilities, such as outdated versions and misconfigurations that can expose our systems to attacks. Staying abreast of SSL advancements and best practices is necessary. By continuously optimizing our SSL implementation, we enhance our security posture and mitigate risks associated with data breaches, thereby fostering a secure online environment where our users can engage confidently.
Two-Factor Authentication Explained
Two-factor authentication (2FA) serves as a vital safeguard in our digital landscape, enhancing security by requiring two distinct forms of verification before granting access to our online accounts. By employing diverse user authentication methods, such as passwords combined with biometric data or one-time codes, we significantly reduce the likelihood of unauthorized access. This layered approach not only bolsters our defenses against cyber threats but also streamlines security accessibility for legitimate users. The implementation of 2FA is progressively essential in our interconnected world, where data breaches are frequent. As we adopt these practices, we enable ourselves to secure sensitive information efficiently, establishing a robust framework against potential vulnerabilities while ensuring a seamless user experience.
Data Protection Practices
As we navigate the complexities of data protection practices, understanding the diverse strategies we can employ is crucial in safeguarding sensitive information. Implementing solid encryption techniques and maintaining stringent access controls helps mitigate the risks associated with data breaches. Additionally, regular audits and vulnerability assessments ensure compliance with regulations like GDPR and PIPEDA, which dictate how we manage personal data. We must also emphasize employee training, equipping our teams with the knowledge to recognize potential threats. Moreover, comprehensive incident response plans allow us to react quickly and effectively in the event of a data breach, minimizing damage. By adhering to these meticulous practices, we position ourselves to protect user data and uphold our commitment to data security.
Mobile Security Considerations
How do we make sure that mobile devices used in our casino operations remain protected against an ever-evolving environment of threats? To address the risks posed by mobile malware, we must implement solid security protocols. Regularly updating our applications is crucial to address app vulnerabilities that cybercriminals exploit. Additionally, we should adopt extensive mobile device management solutions to enforce security policies and manage app integrity across all devices.
Educating our staff about identifying potential threats and secure practices is vital, as human error often leads to breaches. Moreover, periodic penetration testing can help us actively discover and rectify weaknesses within our mobile frameworks. By maintaining this attentiveness, we can strengthen our defenses significantly, ensuring a safer, more resilient casino environment for users.
Continuous Monitoring and Incident Response
While we implement comprehensive security measures, continuous monitoring and incident response remain essential components in safeguarding our casino operations. To ensure strong threat detection, we employ advanced tools capable of analyzing network traffic and user behavior in real-time. This proactive approach allows us to swiftly identify anomalies that https://pitchbook.com/profiles/company/435535-30 may signal security breaches.
When incidents are detected, our incident response team operates carefully, following predefined protocols to mitigate risks effectively. Continuous monitoring doesn't just help in detecting threats; it also shapes our subsequent risk assessments and security strategies. By constantly improving our response mechanisms, we strengthen our preparedness against evolving cyber threats, ensuring that our operations remain secure and compliant with industry standards. Monitoring and response are, therefore, vital to our success.
Frequently Asked Questions
Does Wild Tokyo Casino Share User Data With Third Parties?
We’ve determined that Wild Tokyo Casino distributes user data with third parties, perhaps violating data privacy principles. It’s essential to examine their policies closely, guaranteeing we understand how our information might be employed.
How Can I Reset My Wild Tokyo Casino Password?
To reset our Wild Tokyo Casino password, we’ll utilize the password recovery methods provided. Furthermore, we should adopt account security tips like turning on two-factor authentication to enhance our protection against unapproved access effectively.
What Should I Do if I Encounter Login Issues?
If we face login issues, we'll commence with login troubleshooting steps, checking credentials and browser settings. If unsettled, we'll get in touch with user support for further assistance, ensuring a methodical resolution to our access problem.
Are There Age Restrictions for Wild Tokyo Casino?
Yes, there're strict age restrictions at Wild Tokyo Casino. We must pass age verification to comply with gaming regulations, guaranteeing only individuals of legal gambling age take part, thus maintaining a conscientious gaming environment for all.
How Can I Close My Wild Tokyo Casino Account?
To close our Wild Tokyo Casino account, we should proceed to the account settings, select "account deletion," and reflect on the implications for user privacy. Complying with these steps secures protected and comprehensive management of our personal information.
Conclusion
In summary, our comprehensive security analysis of Wild Tokyo Casino shows a robust framework designed to secure Canadian users. With secure login protocols, sophisticated encryption standards, and the adoption of two-factor authentication, we’ve created a reliable defense against potential threats. Furthermore, our ongoing commitment to data protection practices and mobile security guarantees a protected gaming experience. By regularly monitoring and responding to incidents, we not only protect user privacy but also boost trust among our players.
